 There is no corporation with a wider breadth of development in intellectual properties than the International Business Machines Corporation of Armonk, NY. Long associated as a developer of business technologies, IBM has recently announced a free tool for businesses who want to upload data to Watson Analytics to receive predictive insights. The company is increasing its presence in Indian markets by partnering with dozens of startups, including one trying to develop data technologies to predict instances of crime before they occur. IBM is also involved in efforts to develop more effective health care technologies, as is evidenced by the recent decision by Texas-based biosciences company Caris Life Sciences to use IBM technology to accelerate molecular profiling services for cancer patients.
There is no corporation with a wider breadth of development in intellectual properties than the International Business Machines Corporation of Armonk, NY. Long associated as a developer of business technologies, IBM has recently announced a free tool for businesses who want to upload data to Watson Analytics to receive predictive insights. The company is increasing its presence in Indian markets by partnering with dozens of startups, including one trying to develop data technologies to predict instances of crime before they occur. IBM is also involved in efforts to develop more effective health care technologies, as is evidenced by the recent decision by Texas-based biosciences company Caris Life Sciences to use IBM technology to accelerate molecular profiling services for cancer patients.
In this edition of the Companies We Follow series, we’ve surveyed the recently published patent applications which have been filed by IBM with the U.S. Patent and Trademark Office. All in all, we found a wide assortment of data analysis technologies for business, medical and consumer fields which may likely their way into the corporation’s intellectual property portfolio in the months to come.
We start off with a look at a few inventions for software development projects, specifically for the management of artifacts connected to software development files by applications within development platforms. We discuss a trio of patent applications related to helping businesses make sense of immense data sets, including visualization methods and techniques for answering natural language questions. IBM’s patent applications involve more medical technologies, including a system for determining fraud within health care claims. We also profile one patent application describing a unique method for swaying the voting tendencies of a group of participants within an electronically hosted conference.
[Companies-4]
Electronic Documents: Removing Suspicion Artifacts and eBook Wear and Tear
IBM’s business technologies involve a wide degree of products for managing and editing document files, and the corporation has supported other document software projects, like OpenDocument. A number of the patent applications which we explored during our most recent survey of IBM’s patent filings discussed various document management functions for files ranging from business documents to eBooks.
Suspicion flags can be used by document editing applications to denote changes made to a file and ensure a file’s security, useful for tracking the health of a file during the software development process. Managing large numbers of these suspicion flags, however, is a very time consuming process. We noted a couple of IBM innovations designed to address this issue while maintaining proper levels of file security. U.S. Patent Application No. 20140258981, which is titled System and Method for Managing Traceability Suspicion with Suspect Profiles, would protect a computer-implemented method of generating suspect profiles associated with traceability links between artifacts generated by suspicion flags. The traceability links help to mark changes to artifact characteristics for more effective suspicion flag management. U.S. Patent Application No. 20140258982, entitled System and Method for Tracking Suspicion Across Application Boundaries, would protect another computer-implemented method also designed to better manage suspicion flags and related artifacts. This invention tracks the changes to artifact shapes and application components to determine suspicious relationships between applications within a software development environment.

From U.S. Patent Application No. 20140258839, titled “Systems and Methods for Customizing Electronic Documents Based on Use Patterns.”
A much different type of document file, eBooks, was the focus of an intriguing patent application directed at novel methods for visualizing eBook use in ways that approximate real-life wear. U.S. Patent Application No. 20140258839, titled Systems and Methods for Customizing Electronic Documents Based on Use Patterns, discloses an IBM innovation for customizing an eBook which involves a tracking module to monitor a user’s interaction with an eBook, including time spent reading a certain page, the number of times a page is accessed or repeated magnification of a specific page section. The use indicators that represent the level of user interactivity with a page can include page rips, folds, dirt smudges or discolored edges.
Making Sense of Business Data
As IBM’s decision to offer freeware versions of Watson analytical tools would indicate, the corporation is investing heavily in business applications for analytical software tools which help an organization make meaningful sense of large sets of operational data. A few patent applications in this field showcased interesting technologies on analyzing and visualizing data which are meant to improve a person’s ability to comprehend truly useful aspects of data sets, whether for business operations or otherwise.
Improvements to multidimensional data analysis provided by online analytical processing (OLAP) systems would be protected for IBM through the filing of U.S. Patent Application No. 20140258311, entitled Insight Determination and Explanation in Multi-Dimensional Data Sets. The computer program product that would be protected can identify insights which satisfy relevance criterion as well as reasons pertaining to the identification of the analytical insights. This system would allow users of IBM’s OLAP tools, such as the company’s InfoSphere Warehouse Cubing Services for warehouse facilities, to gain meaningful insights on transactions and other data. A technology that also helps business professionals better grasp displayed data is featured in U.S. Patent Application No. 20140258817, filed under the title Context-Based Visualization Generation. This patent application would protect a method of detecting visualizable subject matter within a data set as well as a context for the data used for the selection of a visualization engine. According to the description of the invention, this technology has been designed to improve the digitization of educational textbooks for providing visualizable subject matter in a range of academic areas, including math, chemistry and geography.
Along with making better sense of business or textbook data, IBM is also involved in creating database technologies for helping users quickly find the answers to important questions. U.S. Patent Application No. 20140258286, which is titled System and Method for Providing Answers to Questions, would protect a computer-implemented method of retrieving answers to natural language questions that involves processing the question to obtain relevant documents, generating candidate answers from those documents and outputting candidate answers based on a confidence score. The invention achieves the objective of providing a dynamic and methodology for receiving questions in a computing environment and providing answers to those questions.
[Companies-3]
Data Analysis Technologies for Health Care
IBM’s technology for molecular profiling in cancer treatments is only one of many technologies for data analysis developed by the company with specific applications to medical fields. A few patent applications in this field caught our eyes today, including one directed at a technology serving to help uncover instances of health care fraud.
Programs for the temporal analysis of electronic medical records in clinical settings have been described in the IBM’s filing of U.S. Patent Application No. 20140257847, entitled Hierarchical Exploration of Longitudinal Medical Events. The computer program product that would be protected by this patent application is designed to determine and group medical events which are co-occurring within a time period to minimize the number of sets of medical data and identify patterns within the medical events. The technology also provides visualization functions which help a physician better diagnose issues related to a series of medical events, such as cardiac events, experienced by a patient. We also noticed a computer-aided audit technique for detecting fraud in the health care industry which was outlined by U.S. Patent Application No. 20140257846, which is titled Identifying Potential Audit Targets in Fraud and Abuse Investigations. The method described involves techniques for analyzing the expected rate of activity in a health care domain focus area among patients, prescribing entities and pharmacies. The computer-aided audit method can determine abnormal levels of activity in interactions among these different entities within a focus area. The innovation is designed to better control the cost of fraud in health care without preventing legitimate health care claims for patients from medical professionals.
Collaborative Workspaces for Increased Productivity
Other than data analysis, the International Business Machines Corporation also provides computing solutions for businesses who want to encourage communication between project teams or enhance collaboration with those outside of an organization. Today, we were intrigued enough to share a couple of IBM patent applications in this field detailing innovation in the field of providing digital workspaces.

From U.S. Patent Application No. 20140258213, filed under the title “Autonomic Collaborative Workspace Creation.”
A product for initializing the preparation of a digital workspace for a collaborative event which cuts down on productivity lost while setting up the collaboration is expressed within U.S. Patent Application No. 20140258213, filed under the title Autonomic Collaborative Workspace Creation. The computer program product that would be protected is designed to track artifact usage over a plurality of collaborative interactions occurring in a plurality of workspaces and analyze tracked artifact usage to determine artifact patterns. This innovation would allow a party to pre-launch a collaborative workspace with applications, documents, team rooms and other artifacts which are relevant to parties involved in the collaboration. Methods of project management over social networks are also developed by IBM and disclosed within U.S. Patent Application No. 20140257894, which is titled Social Project Collaboration Through Self-Organizing Teams. The method for social project collaboration which would be protected is designed to create a graph of nodes representing people and tasks and a function for assigning tasks to users within the social network. This method of providing for social networking collaboration could be implemented through Facebook, Twitter or IBM Connections networks.
Guiding Voting in an Electronic Conference
We’re wrapping up our survey of IBM’s recently filed patent applications with a look at one which would protect one of the more Orwellian technologies that we’ve been able to catch here in IPWatchdog’s Companies We Follow series. U.S. Patent Application No. 20140258393, which is titled Guiding a Desired Outcome for an Electronically Hosted Conference, would protect a system comprised of a processor designed to monitor the activity of participants within an electronically hosted conference and provide a list of participants and recommendations on the order in which to poll the participants to achieve a desired decision outcome. As the description section of the patent application notes:
“Because people oftentimes are influenced by others, polling the participants in a particular order can influence the outcome of the vote. In illustration, if the fifth person being polled is undecided, but the first four people who are polled all vote a particular way, the undecided person may end up voting that same way. Accordingly, polling the participants in a particular order based on participant sentiments can actually influence the votes to achieve the desired outcome.”
The system of this invention provides the participant polling order list to a moderator or chairperson, allowing them to begin the polling in such a way to produce a desired outcome on a voting matter.

![[IPWatchdog Logo]](https://ipwatchdog.com/wp-content/themes/IPWatchdog%20-%202023/assets/images/temp/logo-small@2x.png)

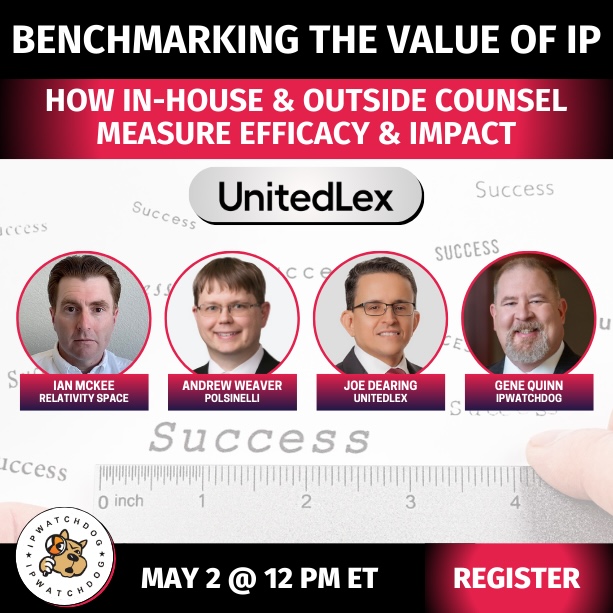
![[Advertisement]](https://ipwatchdog.com/wp-content/uploads/2024/04/UnitedLex-May-2-2024-sidebar-700x500-1.jpg)
![[Advertisement]](https://ipwatchdog.com/wp-content/uploads/2024/05/Quartz-IP-May-9-2024-sidebar-700x500-1.jpg)
![[Advertisement]](https://ipwatchdog.com/wp-content/uploads/2024/04/Patent-Litigation-Masters-2024-sidebar-700x500-1.jpg)

![[Advertisement]](https://ipwatchdog.com/wp-content/uploads/2021/12/WEBINAR-336-x-280-px.png)
![[Advertisement]](https://ipwatchdog.com/wp-content/uploads/2021/12/2021-Patent-Practice-on-Demand-recorded-Feb-2021-336-x-280.jpg)
![[Advertisement]](https://ipwatchdog.com/wp-content/uploads/2021/12/Ad-4-The-Invent-Patent-System™.png)






Join the Discussion
9 comments so far.
Gene Quinn
October 10, 2014 01:59 pmBenny-
You can beg all you want, but you are wrong. PLEASE read the article!
Furthermore, with respect to reading the article, you said: “If you read the article in the link refers to, you quickly learn that they are not trying to do any such thing.”
I know you like to play games, and I am getting tired of your brand of nonsense. The clear implication is that if one reads the article it doesn’t say what Steve says it says. Of course, if you do actually take time to read the article it says EXACTLY what Steve says it says.
Why you are making an issue about his characterization I have no idea, but I’m not about to let you say something that isn’t true. Here is the first paragraph:
“In the American crime drama series Person of Interest, a machine predicts whether a person can be a victim or a perpetrator of a crime. Then it’s up to a data scientist to find that person and prevent any violent acts. This may sound like science fiction but Thiruvananthapuram-based big data startup Senzit is trying to turn this into reality. Its digital recording solution captures and archives live events from crime scenes. It then mines hidden insights, patterns and unknown correlations from the vast amount of data that can be collated this way.”
So Steve’s characterization is perfectly correct. You taking issue with a perfectly correct characterization and then not letting go and defending the indefensible is bizarre to say the least.
-Gene
Benny
October 10, 2014 01:17 pmGene,
I beg to disagree. Nowhere in the article is the suggestion that any company IS actually creating technology which emulates the science fiction TV series mentioned. All references to the software company point to collecting data from a crime scene after the event. Could you quote anything from the article that tells us otherwise?
I’m not suggesting Steve didn’t read the article. “Read” in past tense and present progressive are spelt the same, you can tell from the syntax of my comment that I meant the latter.
Gene Quinn
October 10, 2014 10:59 amNice try with an obscure line from the article that seems to support you, but an article is much more than any one sentence. Rather unbecoming to hunt and search for something, anything that supports your position rather than admit you are wrong.
If you actually read the article, the first several paragraphs deal with exactly what Steve said in this article. You really don’t need to go digging any further than that. There is a reference to “Person of Interest” and making that a reality with technology.
I took issue with you because in a very snarky way you suggested that Steve didn’t read the article he cited. What is clear is that you didn’t read the article, or you selectively bypassed the first few paragraphs that set the entire premise of the article. So your quote taken out of context not withstanding, those who actually follow the link and read the article can come to their own conclusions about whether Steve’s characterization is accurate. I did read the article and I am perfectly fine with Steve’s characterization. I actually find it to be accurate, and clearly far more accurate than your selective reading.
-Gene
Benny
October 9, 2014 03:39 amGene,
Here is the description of the technology from the article itself:
“The two-year-old firm captures all the events of a case from the beginning, which includes audio, text. This way it keeps track of any change of statement or verdict. ”
Nothing in it about preventing crime. It’s all about improving and speeding up the justice system. Which is not neccessarily good news for everyone who earns a living in that field (now THAT was a snarky comment – but you probably know by now that I often let a little cynicsm slip out – it’s never meant to offend).
Gene Quinn
October 8, 2014 04:37 pmBenny-
What a snarky comment. Perhaps it is YOU who needs to go and read the article. The opening paragraph refers to the show “Person of Interest.” The whole premise is that by analyzing vast amounts of data you can prevent crime before it happens. The article explains that IBM is working to make that a reality with a number of start-ups.
Furthermore, what is the point in capturing large sums of data and running analysis to detect patterns? Seems self evident to me that at least an important part of the purpose is to… well… identify patterns that may be useful. Useful how? Do you think those patterns identified might be useful to predict crime before it happens? This is what happens when facial recognition technology meets artificial intelligence and data analytics at the speed of Watson.
Seriously, if you are going to take shots the least you could do is read the article yourself.
-Gene
Benny
October 7, 2014 01:55 amCurious,
I’m not a patent attorney. I work in engineering. I read claim 1 of the application, and to the engineering mind it doesn’t appear to point towards any machine transformation, rather to an abstract idea. Knowing that many of the readers of this blog ARE patent attorneys, I specifically requested to be corrected if I misunderstood the claim. If you have expertise in the legal field, why are you asking an engineer for his analysis on legal matters, instead of providing an explanation?
Curious
October 6, 2014 03:19 pmUS20140257894 appears to be an attempt to patent an abstract idea – claim 1 does not seem to refer to patent eligible subject matter (correct me if I am wrong)..
Why don’t you expound upon YOUR analysis?
Gene, but not Gene Q
October 6, 2014 08:19 am“If you read the article in the link refers to, you quickly learn that they are not trying to do any such thing. They are developing an event database/data- correlation package for use AFTER the event.”
whew! i was afraid that Lamar Burgess was incarnating at IBM.
Benny
October 6, 2014 07:59 am1. “….including one trying to develop data technologies to predict instances of crime before they occur…”
If you read the article in the link refers to, you quickly learn that they are not trying to do any such thing. They are developing an event database/data- correlation package for use AFTER the event.
2. US20140257894 appears to be an attempt to patent an abstract idea – claim 1 does not seem to refer to patent eligible subject matter (correct me if I am wrong).